Areas of Specialization
Assessments | CISOaaS | Compliance Review | Enterprise Architecture | Gap Analysis | Network & Security Monitoring | Policy Development | Remediation | Scanning | Vendor Evaluation
Why Garnet River for Cyber and Information Security
Large and small organizations alike face the risks of information security breaches. The potential losses are substantial, with the average quantifiable cost for a data breach in the U.S. being $4.24MM (IBM), not to mention the qualitative cost of reputational harm.
At Garnet River we recognize security is not a point in time solution. We work with clients to develop processes that mitigate risk and enable the scalable, secure handling of information to operational, information, practical, and educational security needs.
Garnet River also brings a unique multidisciplinary approach to data security and privacy. We understand the requirements, because we have foundational expertise in data security, infrastructure, and privacy. But we also understand the why and how…and that the right people paired with a technology-supported process makes assessment, analysis, action planning, and remediation efficient and effective.
Our practice lead is an (ISC)² security influencer and was lead information security architect for the U.S. Federal Reserve. We back him with information security engineers, technical architects, legal and compliance officers, and communications specialists.
The reason for this multidisciplinary approach: Information Security decisions are increasingly being made in the boardroom. That’s why your security staff needs greater exposure to the business, and the business needs to see the security staff as a partner that can align objectives with organizational imperatives.

“Information security is a journey, not a destination. Compliance is not an end state but a checklist that provides direction for the journey. At Garnet River, we help clients navigate this journey. We emphasize the basics, but we complement them with a strong information security program, technical tools, and sound policy…all while mapping progress and remediating issues along the way.”
– Michael D. Weisberg, Practice Lead
Our Offerings & Programs
CISO as a Service
K-12 Data Security and Privacy
NYDFS Security Program
Products
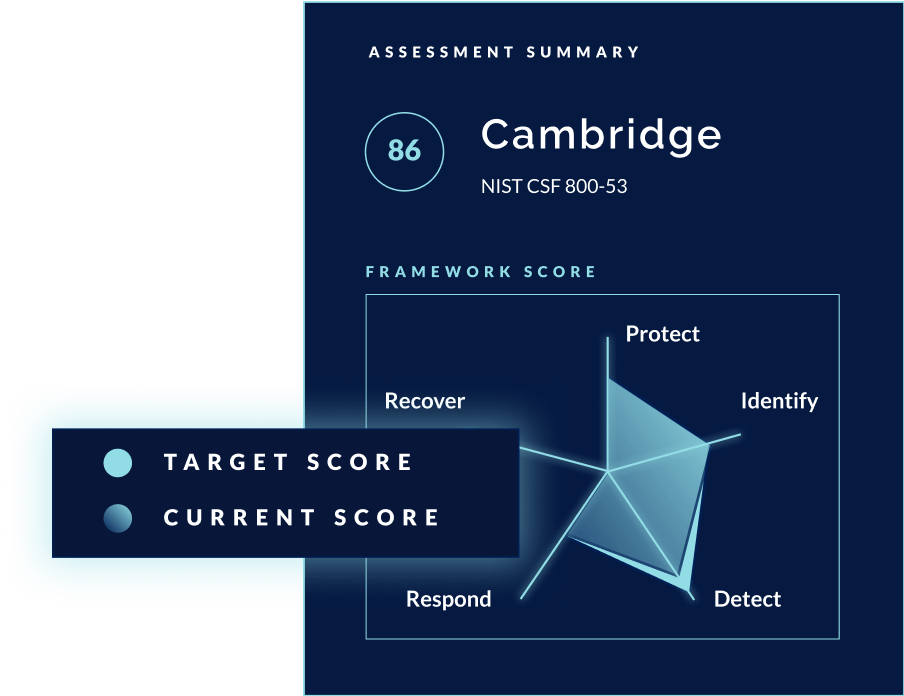
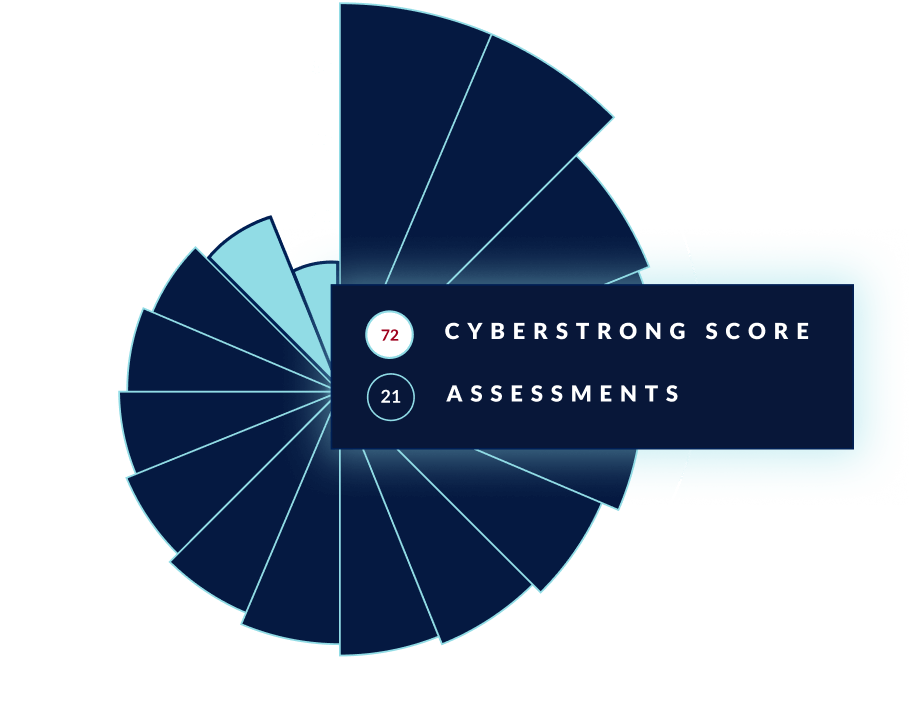
Security…Powered by Platform
Much of our security program is delivered on a proprietary platform that offers standardized mapping across frameworks, centralized risk and compliance data, and automated cyber and IT risk management. It’s technology done right: easy, transformative, and insightful.