What is SAAP? It is Security as a Process
Security as a Process (SAAP) and the classification of information is fundamental to information security. This article, the second in a three-part series, looks at the "how" of information security and why it is so important.
Reading time: 2 minutes
“If you can’t describe what you are doing as a process, you don’t know what you’re doing.”
— W. Edwards Deming
In the last article, we looked at how policy and standards influence the information security governance environment. They provide the foundational framework on which you hang the tasks of information security.
The next step in governance is to establish documented, repeatable processes to enable the rapid and consistent application of security in your environment. Consistent process not only improves an organization’s overall posture but also defines the patterns of action that can be used to advance the forensics, business continuity and incident response environments.
Processes Describe “How”
So far, we’ve looked at documents describing the “why” and “what” of information security, now we arrive at the level of “how.” We are not talking about the step-by-step details of a procedure but rather a description of repeated actions that can be used to ensure that an action is taken in a repeatable manner. An example would be a process to describe the clearing of an alert from a console:
- When alerts are to be cleared from the console, an entry shall be made in the event log.
- The entry will describe the alert and what action was taken to resolve the alert.
- The entry will contain the alert number, the alert description, the data, time and name of the operator clearing the alert.
- Cleared alerts shall be reviewed with the shift manager at the end of each shift.
Note the level of detail. Again, this is not a procedure, which dictate the steps to be taken, but rather a description of what must be done and how it must be done.
Keep It Simple
While policies and standards can become very detailed, and are often expressed in business terms, processes are a technical manifestation of the business’s needs. Often, the best way to express a process is via a process diagram. Below is a sample diagram on the process for classifying information:
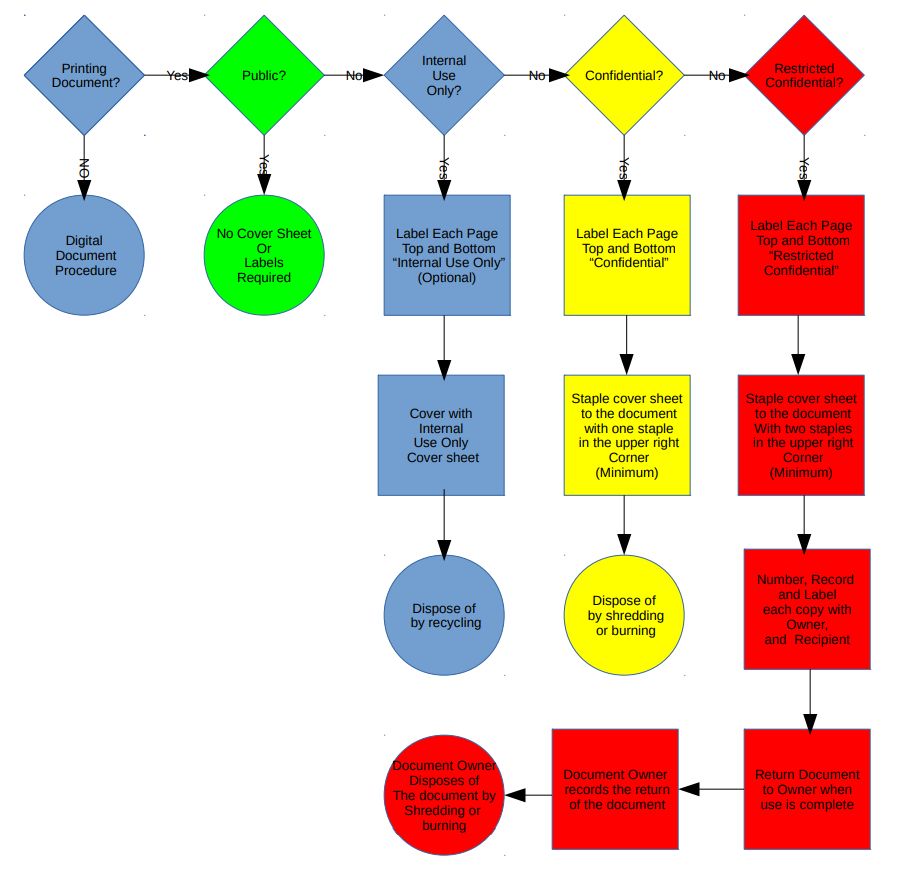
Notice that the process does not go into the technical detail, but it explains each step required to classify the information. This provides clarity and allows technical organizations to derive the procedures that they will use to implement the process.
In the next article, we will discuss how procedures, practices and guidelines complete the documentation suite and how they lead to repeatable architectural design patterns for security and an information security governance pyramid.
This is part 2 of a 3-part series.
1. The Secrets Behind Information Security Organization
2. What is SAAP? It is Security as a Process
3. Three Elements that Complete the Governance Pyramid

Michael D. Weisberg, CISSP, CSM, is Vice President of Information Security and Assurance Services at Garnet River LLC and the Director of Cyber Security Programs at the School of Professional and Continuing Education at the Sage Colleges in Albany, NY. As an information security leader and subject matter expert, Michael has been a contract CISO for several organizations.


