Four cybersecurity operations you can automate
Most CIOs expect their involvement in cybersecurity to increase over the course of 2023. Many are using AI. Automation can support full-scale SOAR across a number of areas.
Reading time: 3 minutes

According to Foundry’s State of the CIO Study 2022, 76% of CIOs anticipate their involvement in cybersecurity to increase over the next year, with 51% saying they are currently focused on security management in their role.
While many CIOs currently use artificial intelligence applications for IT operations (AIOps) and security operations (SecOps) to continuously improve the security posture of their organizations, few of these tools enable end-to-end security operations automation.
Why does robotic process automation (RPA) matter?
Time and fatigue. On any given day, cybersecurity engineers may be defining and enforcing security rules and policies; scanning for threats, monitoring for vulnerabilities, and mitigating attacks; and conducting continuous security audits and tracking access control to critical resources.
A team can only handle so many threat alerts before they start to get missed. In fact, Cybersecurity Dive reports that “more than one-third of IT security managers and security analysts ignore threat alerts when the queue is full.”
RPA, by using bots to replace repetitive manual tasks done by humans, streamlines and speeds up process—with greater accuracy and reliability. It can also support full-scale security orchestration, automation, and response (SOAR) across a number of areas, including: identity lifecycle; threat detection and prevention; incident response; and audit and compliance.
Identity lifecycle
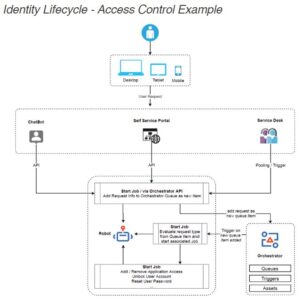 Within most companies, IT analysts manage user profiles, roles, and employee access controls. Some of their activities may include user provisioning, adding/removing application access, resetting user passwords, and unlocking user accounts. These activities can be managed with automation.
Within most companies, IT analysts manage user profiles, roles, and employee access controls. Some of their activities may include user provisioning, adding/removing application access, resetting user passwords, and unlocking user accounts. These activities can be managed with automation.
API capabilities can expand to the service management area (i.e., IT service management (ITSM) tickets). The robot can start jobs based on the defined trigger, perform necessary user management actions, update the ITSM ticket, and inform the user about the resolution.
By automating user management activities, one partner ITOps team reduced their workload by more than 15%. Also, the average handling time of ITSM tickets came down from two hours per ticket to just two minutes per ticket. That translates to a 98% decrease in time spent on resolving tickets, freeing the team up for more complex tasks.
Threat detection and prevention
Another key focus for security professionals is detection and prevention activities. Per a recent IBM study, “organizations with a ‘fully deployed’ security automation strategy had an average breach cost of $2.90 million – whereas those with no automation experienced more than double that cost at $6.71 million.”
Using event-driven automation capabilities, a robot can be triggered from the endpoint detection and response (EDR), extended detection and response (XDR), security information and event management (SIEM), or other security monitoring tools to perform remediation actions.

Automations can also manage brute force attack alerts. One partner blocks more than 20,000 brute force attacks each year using automations. In addition, you can automate processes that touch multiple systems, including ticketing for top system vulnerabilities that utilize enterprise systems like Tableau, Tenable, ServiceNow, and SharePoint.
Incident response
Incident response management is the true test of a security team’s robustness.
Timing is of the essence in case of any breach. According to an IBM study, “companies with an incident response team that also tested their incident response plan had an average breach cost of $3.25 million, while those that had neither in place experienced an average cost of $5.71 million (representing a 54.9% difference.)”
Activities that can be automated as part of an incident response plan include:
- Deleting or quarantining suspicious malware-infected files
- Performing a geolocation lookup on a given IP address
- Searching for files on a particular endpoint
- Blocking a URL on perimeter devices
- Quarantining a device from the network
- Retrieving information about any compromised users
These activities help accelerate remediation as well as standardize incident response processes.
Audit and compliance
All organizations must perform various audits and ensure compliance against industry standards such as SOX, HIPAA, and GDPR. As part of an audit, teams need to collect evidence, map information, and perform controls testing and assessment. Many of these activities can be automated, such as:
- Pulling a list of all AD users by groups, role memberships, and resource ownerships
- Validating separation of duties across application development and deployment processes
RPA can also be used to monitor compliance needs. Instead of waiting until annual auditing activities, robots can proactively stop any control failures and alert respective managers, as well as provide notifications of any compliance violations.


